Protocols
Introduction
- The two main protocols used to ensure security when using the internet are Secure Sockets Layer (SSL) and Transport Layer Security (TLS); these are both part of the transport layer discussed in Chapter 14.
- TLS is the more modern; it is based on SSL.
- The primary use of SSL and TLS is in the client/server application (see Chapter 2).
- They both use the standard cryptographic protocols to ensure there is a secure and authenticated communication between client and server.
- However, normally only the server is authenticated with the client remaining unauthenticated.
- Once a secure link between server and client is established, SSL or TLS protocols ensure no third party can eavesdrop.
Secure Sockets Layer (SSL)
When a user logs onto a website, SSL encrypts the data – only the client’s computer and the web server are able to make sense of what is being transmitted.
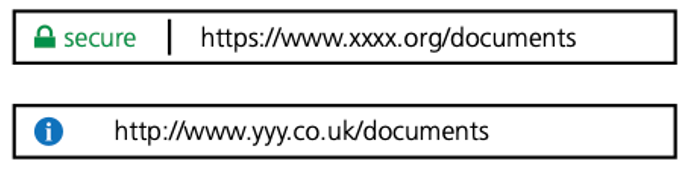
Two other functions of SSL are data compression (reducing the amount of data being transmitted), and data integrity checks. - A user will know if SSL is being applied when they see the https protocol and/or the small green closed padlock.
Examples of where and when SSL (and TLS) would be used include
- online banking and all online financial transactions
- online shopping/commerce
- sending software to a restricted list of users
Transport Layer Security (TLS)
Transport Layer Security (TLS) is a modern, more secure version of SSL – it provides encryption, authentication and data integrity in a more effective way.
It ensures the security and privacy of data between devices and users when communicating over a network (such as the internet).
When a website and client communicate over the internet, TLS prevents third party eavesdropping.
TLS is formed of two main layers:
- Record protocol can be used with or without encryption (it contains the data being transmitted over the network/internet).
- Handshake protocol permits the web server and client to authenticate each other and to make use of encryption algorithms (a secure session between client and server is then established).
Only the most recent web browsers support both SSL and TLS, which is why the older, less secure, SSL is still used in many cases (although soon SSL will not be supported and users will have to adopt the newer TLS protocol if they wish to access the internet using a browser).
It is possible to extend TLS by adding new authentication methods (unlike SSL).
TLS can make use of session caching which improves the overall performance of the communication when compared to SSL (see below).
TLS separates the handshaking process from the record protocol (layer) where all the data is held.
Session caching
- When opening a TLS session, it requires considerable computer time (due mainly to complex cryptographic processes taking place).
- The use of session caching can avoid the need to utilise as much computer time for each connection.
- TLS can either establish a new session or attempt to resume an existing session; using the latter can considerably boost the system performance.
Summary
As already indicated, two of the main functions of SSL/TLS are
- the encryption of data
- the identification of client and server to ensure each knows who they are communicating with.
Stage 1: Once the client types in the URL into the browser and hits the <enter> key, several steps will occur before any actual encrypted data is sent; this is known as the handshaking stage.
Stage 2: The client’s browser now requests secure pages (https) from the web server.
Stage 3: The web server sends back the SSL digital certificate (which also contains the public key) – the certificate is digitally signed by a third party called the certificate authority (CA) (see Section 17.4.2).
Stage 4: Once the client’s browser receives the digital certificate, it checks
- the digital signature of the CA (is it one of those in the browser’s trusted store
- a list of trusted CAs is part of the browser which the client downloads to their computer)
- if the start and end dates shown on the certificate are still valid
- if the domain listed in the certificate is an exact match with the domain requested by the client in the first place.
Stage 5: Once the browser trusts the digital certificate, the public key (which forms part of the digital certificate) is used by the browser to generate a temporary session key with the web server; this session key is then sent back to the web server.
Stage 6: The web server uses its private key to decrypt the session key and then sends back an acknowledgement that is encrypted using the same session key.
Stage 7: The browser and web server can now encrypt all the data/traffic sent over the connection using this session key; a secure communication can now take place.